Transportation technology and the unknown
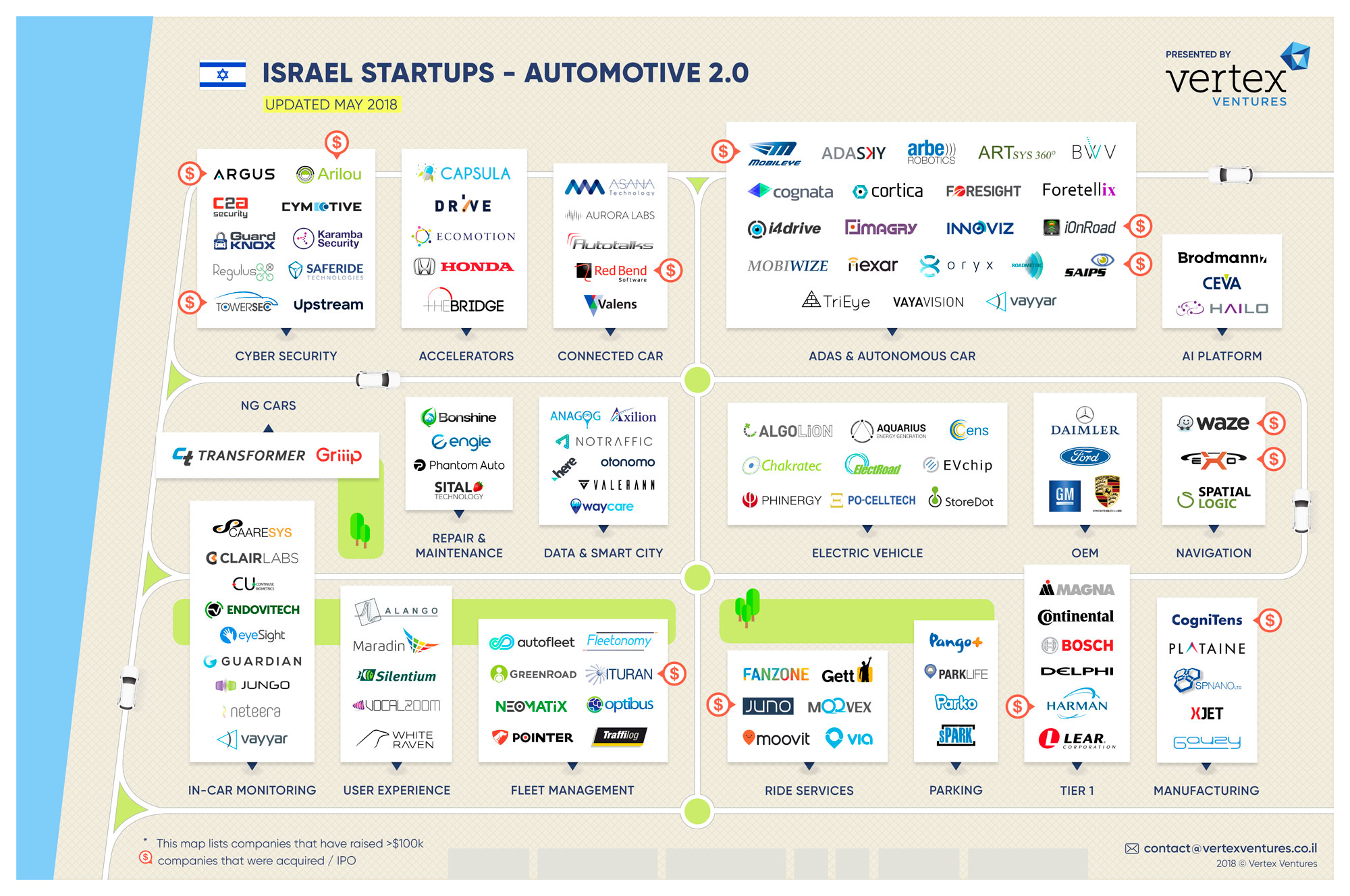
"When I was a kid" is the beginning of many a discussion on how things were better in past generations. Obviously, obviously, it was better to play outside than to watch television. The effects of technology on people, such as how using social media affects our brains is a common discussion point today. Are we living in a bubble or echo chamber? These are all interesting perspectives on the effect of new technology on our brains, but there's a more physically visible effect of technology on our lives, and perhaps it illustrates similar effects. One of the biggest categories of tech companies getting funded these days is transportation. Uber's $72 billion valuation may grab the headlines, but other companies like Lyft, Didi, Grab, Ola, Gett, and Go-Jek are all valued over a billion dollars and targeting the ride-hailing/taxi space. As an aside I wrote of the tendency of companies to compare themselves to Uber back when Uber was only an $18 billion company in Uber meets Pretty Woman. For anyone who lives in an area underserved by public transportation and/or taxi service, these ride hailing services have made many people's lives easier. One can argue if the lives of the…